Discover SPIKE
What is SPIKESpike is a protocol fuzzer creation kit. It provides an API for creating your own fuzzers for network protocols, using the C++ language. SPike provides a series of basic commands for generating fuzzed messages to be sent to a network service. Scriptiong SPIKEFor TCP-based server applications, we use scrpit .spk with the generic_send_tcp interpreter (preinstalled on Kali Linux). The basic syntax is : 1generic_send_tcp <IP> <port> <script.spk> <SKIPVAR> <...
THM - BOF - Task8
Step 1: Find the offsetThe first step is to find the offset that will allow us to replace the return address. To do this, there are 2 methods: Manual method:We can see in the source code that the buffer is 140 bytes long, but between the end of this buffer and the return address there are possible fill bytes (memory alignment) and the rbp register (base pointer), which is 8 bytes long on a 64-bit architecture.So, to overwrite the return address, you’ll need at least 148 bytes. To find out the...
THM - BOF - Task7
Source : https://tryhackme.com/room/bof1 The aim of this exercise is to modify the normal operation of the program so that it executes a function that it is not supposed to be able to execute. After connecting to the machine via ssh, we find the program’s c code: 1234567891011121314151617181920void special(){ printf("this is the special function"); printf("you did this, friend!\\n");}void normal(){ printf("this is the normal function");...
Token Impersonation
A token is a temporary key that enables you to access a system or network without having to give credentials every time you access a resource. These tokens contain information such as : User identity Groups to which the user belongs User privileges There are two types of token: Delegate: Created when a user logs on to a machine or connects to a machine via RDP, these tokens enable a user to usurp the identity of a user on another machine on the network (e.g. a service accessing files on an...
THM - U.A High School
Machine presentation Level: Easy Link: https://tryhackme.com/r/room/yueiua Tools nmap fuzz dirb hexeditor steghide openssl EnumerationWe start with a simple nmap scan: 2 ports are open, the ssh port and the http port.Using dirb, we discover an index.php file in an assets directory, which is unusual: We then try to verify the existence or otherwise of an input parameter to this php file using FUZZ with this command : 1ffuf -u 'http://10.10.85.246/assets/index.php?FUZZ=whoami' -...
THM - Robots
We start with an nmap scan: The robots.txt file reveals 3 directories. Only one of them is accessible:You can now create an account and the initial password will be md5(username+ddmm)So we create a test account with a date of birth of 00/00/0000. We can then calculate the requested hash with the following bash command:Use -n to avoid line breaks. You can then connect to the test account with this password:We can see that the admin account has recently logged in, and we can also see ...
THM - Reset
This challenge simulates a scenario where you have to compromise an Active Directory environment.Scan nmap : In view of the open ports, we’re probably dealing with an Active Directory environment. We can try to obtain information using a few important ports: Port 53 (DNS) :The nmap scan provides us with FQDNs (Fully Qualified Domain Names) such as haystack.thm.corp. We can then ask DNS to provide us with all DNS records linked to the thm.corp domain. This can be done with the dig utility (di...
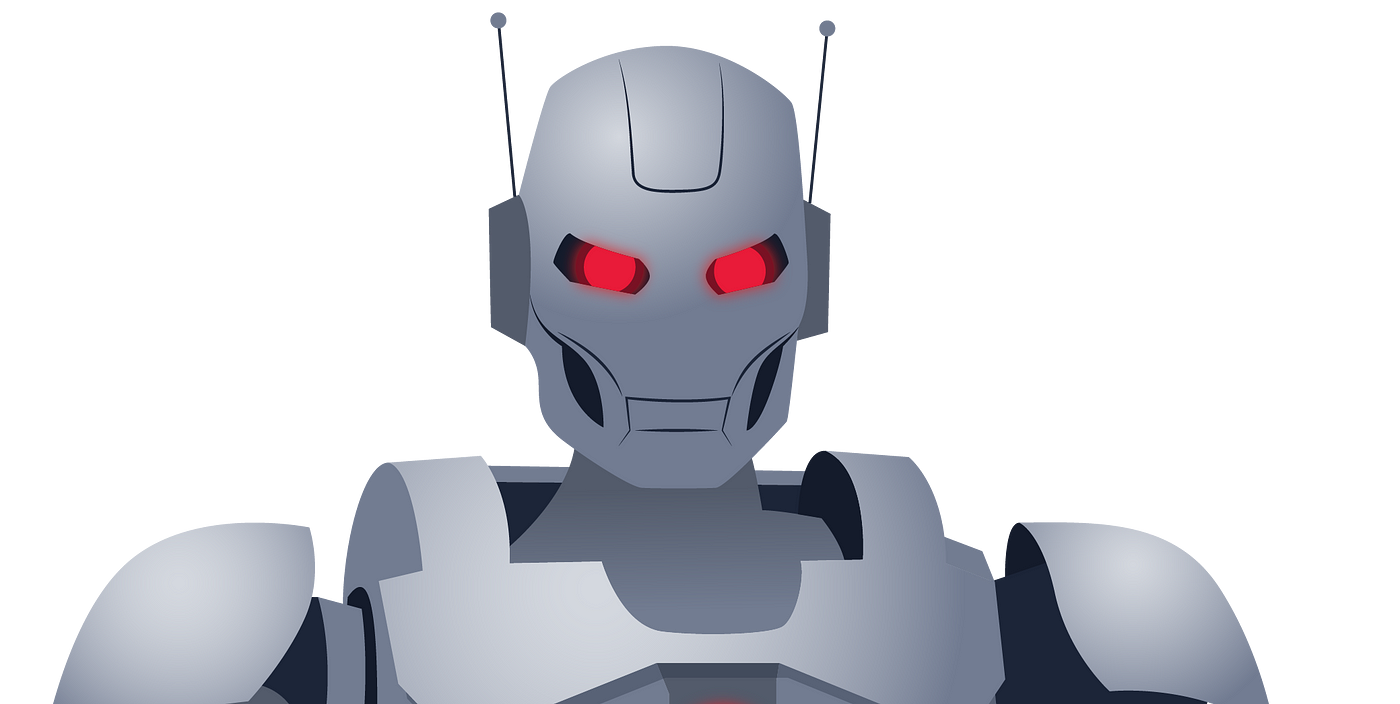
SMB
DefinitionServer Message Block (SMB) is a protocol for sharing files, accessing printers and other resources on a network. It is generally present on ports 445 and 139. It is natively included on Windows. For Linux machines, it is necessary to first install a Samba server, as Linux does not use this protocol by default. SMB enumerationSMB enumeration aims to discover the different shares available on the network, the access permissions to the share and the users and groups present on the mac...
The PrintNightmare
DefinitionPrintNightmare is an attack exploiting a vulnerability in the Windows print spooler which allows a simple user to execute remote commands with administrator privileges. The term PrintNightmare actually refers to two vulnerabilities exploiting the print spooler. One allows privilege escalation and the other allows remote code execution. In this article, we’ll focus solely on the latter. On June 7, 2021, Microsoft released its latest security patch for this vulnerability, which allows...
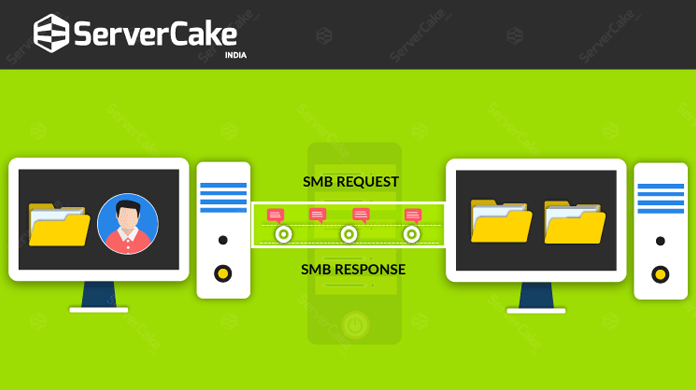
NTLM Relay
DefinitionThe NTLM protocol is an old authentication protocol used by Windows machines to authenticate at domain or network level. It’s a Challenge / Response protocol, so it lets you authenticate to a server without the password ever passing over the network. This protocol is widely used by companies in conjunction with the Kereberos protocol. Only companies with a good cyber maturity no longer use it, as it’s not easy to do without. How it worksWhen a client wants to authenticate to a ...